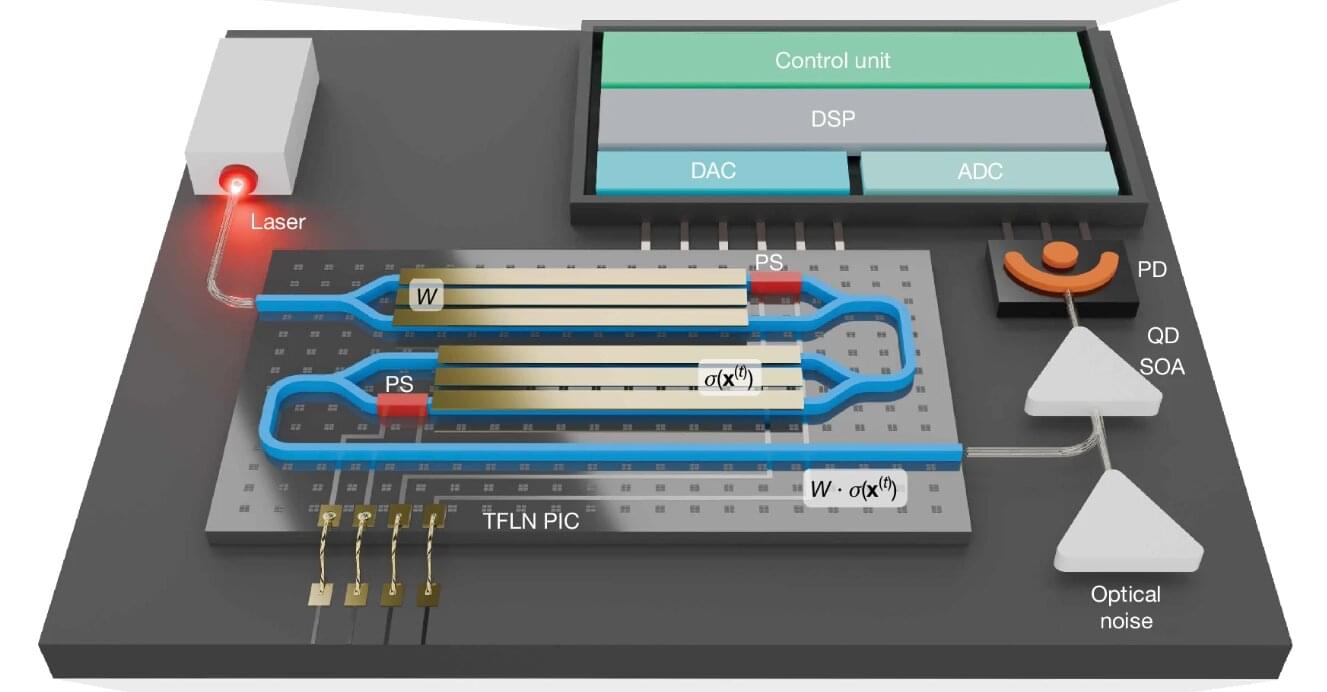
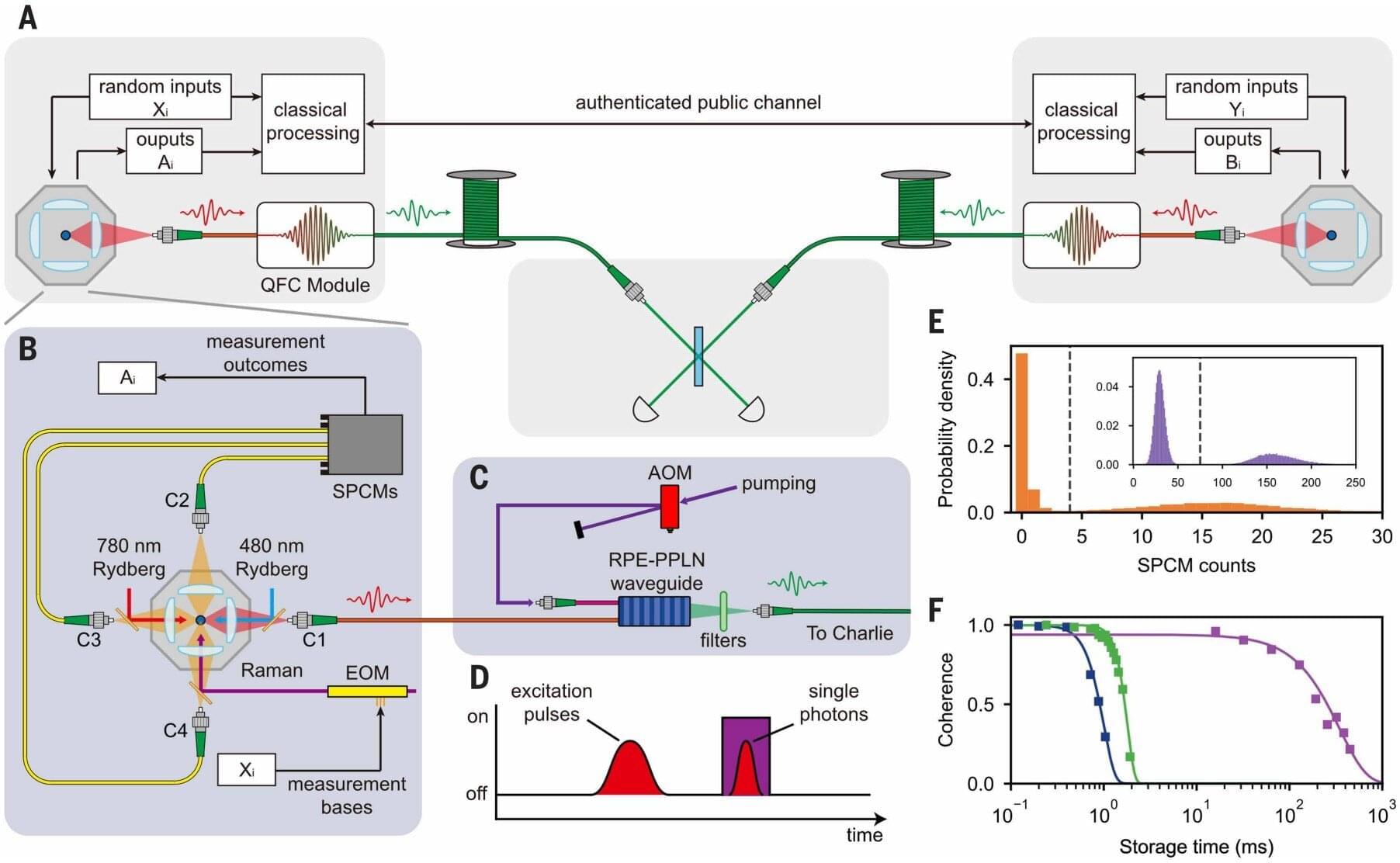
As quantum computers continue to advance, many of today’s encryption systems face the risk of becoming obsolete. A powerful alternative—quantum cryptography—offers security based on the laws of physics instead of computational difficulty. But to turn quantum communication into a practical technology, researchers need compact and reliable devices that can decode fragile quantum states carried by light.
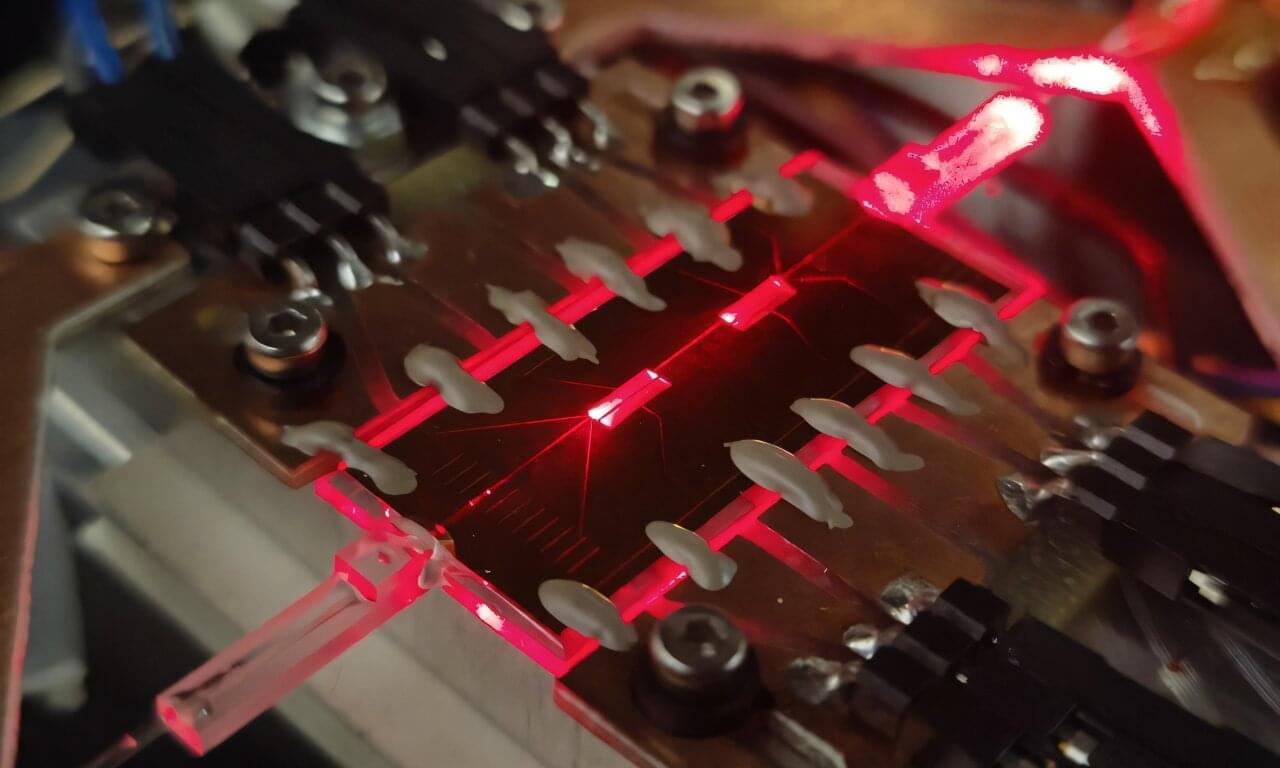
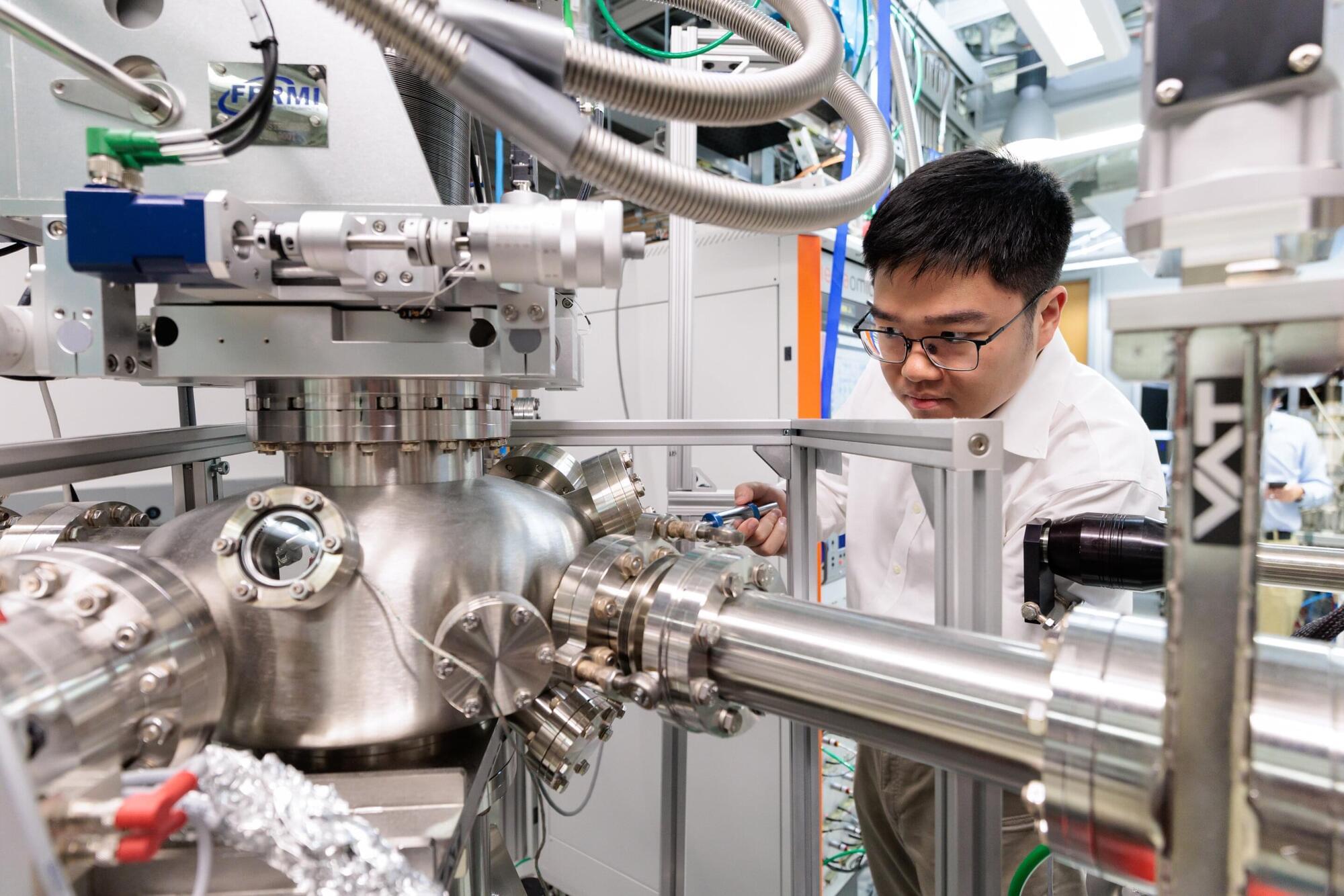
A new study from teams at the University of Padua, Politecnico di Milano, and the CNR Institute for Photonics and Nanotechnologies shows how this goal can be approached using a simple material: borosilicate glass. As reported in Advanced Photonics, their work demonstrates a high-performance quantum coherent receiver fabricated directly inside glass using femtosecond laser writing. The approach provides low optical loss, stable operation, and broad compatibility with existing fiber-optic infrastructure—key factors for scaling quantum technologies beyond the laboratory.